At sċȳr, we deliver end-to-end deployments of cyber-physical systems that are production-ready, aligned to customer requirements, and fully validated before handover. Whether white-labelled under your brand or delivered as a certified partner, our teams integrate with your delivery motion to accelerate time‑to‑value and reduce internal load.
Our services include
Deployment Planning & Readiness
We establish a shared understanding of scope, success criteria, and constraints so delivery starts on solid ground. Readiness covers people, process, and environment to de‑risk execution.
Discovery workshops and requirements validation
Site surveys (remote/on-site), environmental checks, and access logistics
Architecture alignment, BoM validation, and risk/assumption logs
Installation & Configuration
We install, configure, and baseline your solution in line with the approved design and security standards. The outcome is a stable build ready for integration and testing.
Hardware/software installation and baseline configuration
Secure connectivity, identity/access alignment, and data path enablement
Policy/templates set‑up per customer standards (change, backup, logging)
Integration with Enterprise & OT
We connect the platform into the customer’s identity, data, and operational tooling across IT and OT. Integrations are documented and verified end‑to‑end.
Directory/identity, SIEM/SOAR/ITSM, CMDB, ticketing, and notification hooks
OT protocol enablement, data collectors/sensors placement, and tagging strategy
Runbook updates for SOC/operations handoffs
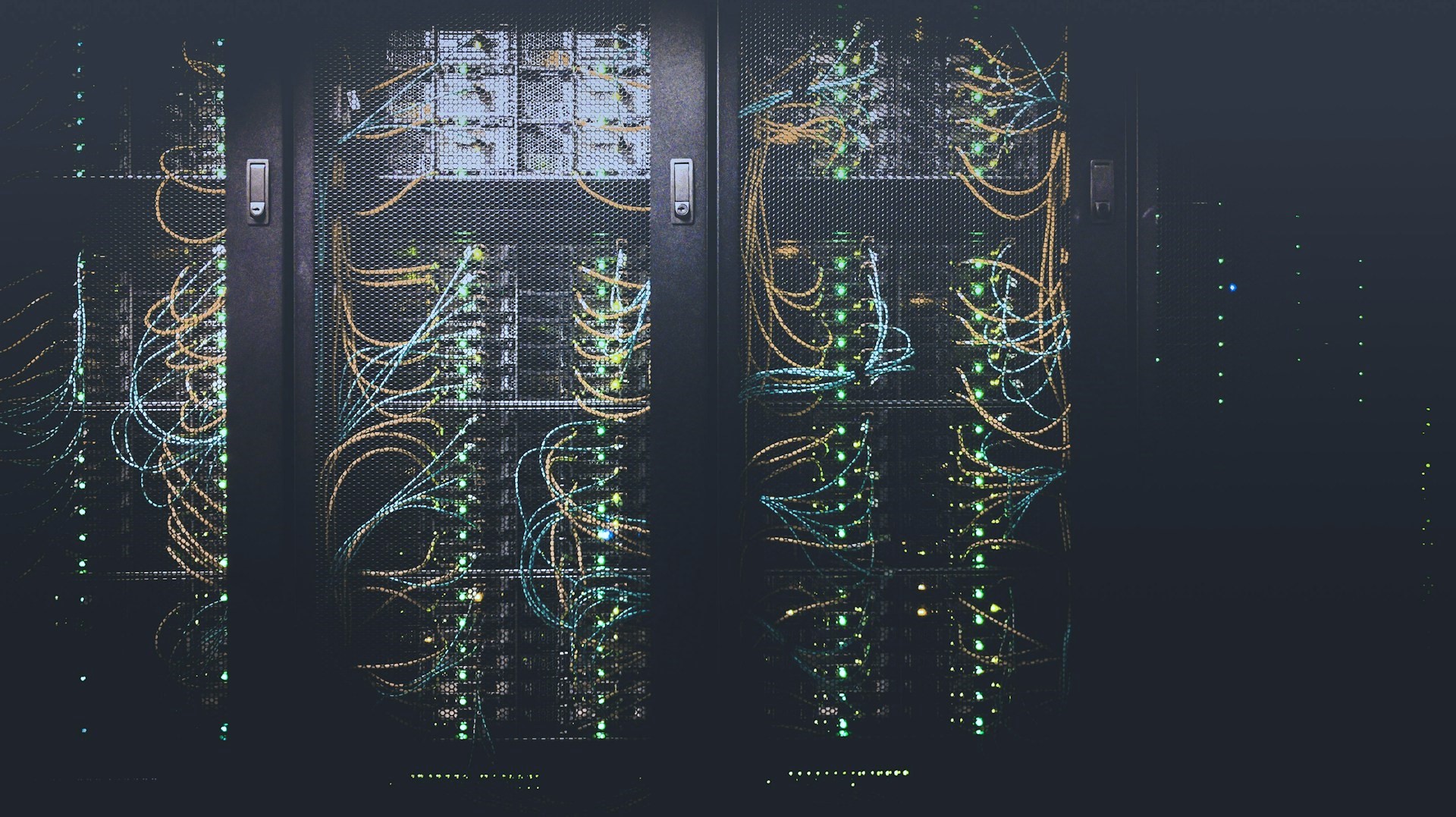
Network Monitoring and Management
Our network monitoring and management services provide real-time visibility and proactive management to maintain network health. We offer:
- 24/7 network monitoring
- Performance analysis and optimization
- Automated alerts and incident management
- Routine maintenance and updates
- Reporting and analytics
Validation & Cutover
We prove functionality, performance, and resilience against acceptance criteria before switching live. Cutover is planned with rollback and supported by hypercare.
Functional testing, performance baselines, and acceptance criteria sign‑off
Failover/DR checks and rollback plans
Hypercare window covering the initial run period
Security Hardening & Compliance
We apply secure baselines and produce evidence for audits. Controls align to customer frameworks and least‑privilege principles.
Secure configuration baselines, privileged access, and key management
Logging, monitoring, and audit readiness for customer frameworks
Evidence packs for customer acceptance and internal QA
Documentation & Handover
We deliver clear, usable artefacts so operations can own the platform confidently from day one.
As‑built diagrams, parameter sets, credentials escrow, and runbooks
Knowledge transfer to customer/resident teams
Final acceptance and transition checklist
Delivery Options
Choose the engagement model that fits your business and your customer.
White‑label delivery under your brand or as a certified deployment partner
Remote‑first with on‑site options for install/cutover as required
Global coverage from a vetted pool of senior practitioners